Cyber crime reached unprecedented levels in 2017! The year saw several key digital security events that included data breaches, ransomware attacks and various other digital criminal activities that increased nearly 28% from 2016, and ultimately cost an annualized average of $11.7M.
Table of Contents
II. Ransomware: The New Normal of Cyber Crime
III. We’re Not Just Phishing Around
IV. Manipulation Through Social Engineering
Sadly, the trend is only increasing with criminal enterprises becoming more adept at utilizing new business models, such as ransomware-as-a-service (RaaS). Cyber crime is no longer the neighbor’s young kid hacking your WIFI or sniffing out your Instagram password while at Starbucks. Criminal enterprises around the world have leveraged new skills in cyber crime, and the primary focus for the foreseeable future will obviously be large organizations, but small and medium-sized businesses are the next logical target. It is estimated that more than half of all cyberattacks committed in 2019 will focus on small to medium business.
Ponemon Institute estimated, in 2017, the average malware attack costs companies an average of $2.4M. Furthermore, it took an average of 50 days to resolve malicious insider attacks and 23 days to resolve ransomware attacks. Those statistics are frightening when a business owner or executive considers how much 20 to 50 days truly costs their organization outside of the realized cost to directly combat the identified problem. Additionally, it is important to understand that cyber crime costs are not solely financial. It also includes lost productivity, theft of intellectual property, wrongful acquisition of sensitive personal data, disruption of post-attack data forensics and even malicious character defamation. The totality of this growing problem can truly seem overwhelming but arming yourself with knowledge enables you to fight this persistent epidemic.
I. Notable 2017 Cyber Attacks
It is no shock that some of the highest profile attacks in 2017 were conducted against very well- known organizations. The reasoning for this year’s attacks are based on a couple of logical key factors. Those high-profile organizations have large repositories of data and vast fiscal capacity, and to criminals that translates into unlimited volumes of data and an easy payday. Below are some of the largest data breaches reported throughout last year.
EQUIFAX: Part of the ‘big three’ in credit reporting, Equifax suffered a massive breach that spanned four months impacting nearly 149 million consumers or nearly half of the population of the United States. The Equifax breach represents much more than just the loss of data or compromised account information. The types of data taken from the credit agency have the potential to do considerable damage if used illegally. Albeit, Equifax remains a top discussion point in news headlines today, their loss wasn’t the largest in history. That honor is bestowed on our next point of discussion.
YAHOO: This was a problem that just didn’t want to go away. What started, in 2013, as a minor breach of 1 million accounts grew to all 3 Billion Yahoo accounts after Verizon acquired the tech giant. The complete compromise that spanned over three years likely provided an endless stream of data from members of the U.S. Congress to members of the FBI, NSA and CIA and even the White House. This epic data breach is the largest in history, to date, and will likely never reveal the true costin terms of lost data.
UBER: What started in 2016, and initially covered up by the company, ultimately grew to a massive problem that exposed the names, phone numbers and e-mail addresses of more than 57 million U.S. subscribers to Uber Technologies Inc’s service. Even worse, Uber’s CEO paid $100,000 to hackers with assurances that the stolen data would be destroyed. The whole situation was more bad press for the company that seemed to be mired in toxic corporate leadership, autonomous vehicle accidents and declining ridership.
VERIZON WIRELESS: Nearly 14 Million U.S. Customers personal details were compromised after NICE Systems, a third-party vendor for Verizon, had inadvertently left sensitive data on an open server. The exposed data included customer names, phone numbers and account Personal Identification Numbers (PIN). All of the data breached was initially found on an unprotected Amazon storage server by a separate security firm who intern notified Verizon of the situation.
INTERNAL REVENUE SERVICE (IRS): The federal tax-collecting agency had been subjected to an intrusion through a data
retrieving tool for the IRS’s Free Application for Federal Student Aid. It is estimated that approximately 700,000 individual’s taxpayer information may have been compromised, thus allowing hackers to file nearly 8,000 applications and steal $30 Million from the U.S. Government. The IRS wasn’t the only federal agency that experienced a digital security event. The Departments of Defense, Labor and State all reported suspected compromises resulting in untold losses of data and funding.
WANNACRY RANSOMWARE: This worldwide hacking attack also commonly referred to as ‘ransomware’ brought more than 200,000 computer systems spread out over 150 countries to a halt. Victims that included hospitals, banking institutions and telecommunications corporations were held hostage and forced to pay a ransom that started at $300, but gradually increased over time with the threat data would be deleted if the ransom wasn’t paid. CNET reported on the attack in mid-2017, and called it, “one of the most prolific cyberattack ever around the globe”. WannaCry’s destruction started from a simple National Security Agency hacking tool that was combined with normal malware to function with worm-like capabilities.
These are just a few of the many events that actually occurred, but the serve as a very sobering reminder that the threat will continue to grow. The Herjavec Group estimates that cyber crime will cost $6 Trillion annually by 2021, which translates to the largest transfer of economic wealth in history. Information Security and even Cybersecurity are terms that everyone must become intimately familiar with. Unlike a computer system on a network, humans cannot be patched or updated. Corporations must adopt methods that meet the psychological needs of employees and relate how cyber crime can and does impact them. Much like a heard of gazelles traversing the African Serengeti, there is safety in numbers.
II. Ransomware: The New Normal of Cyber Crime
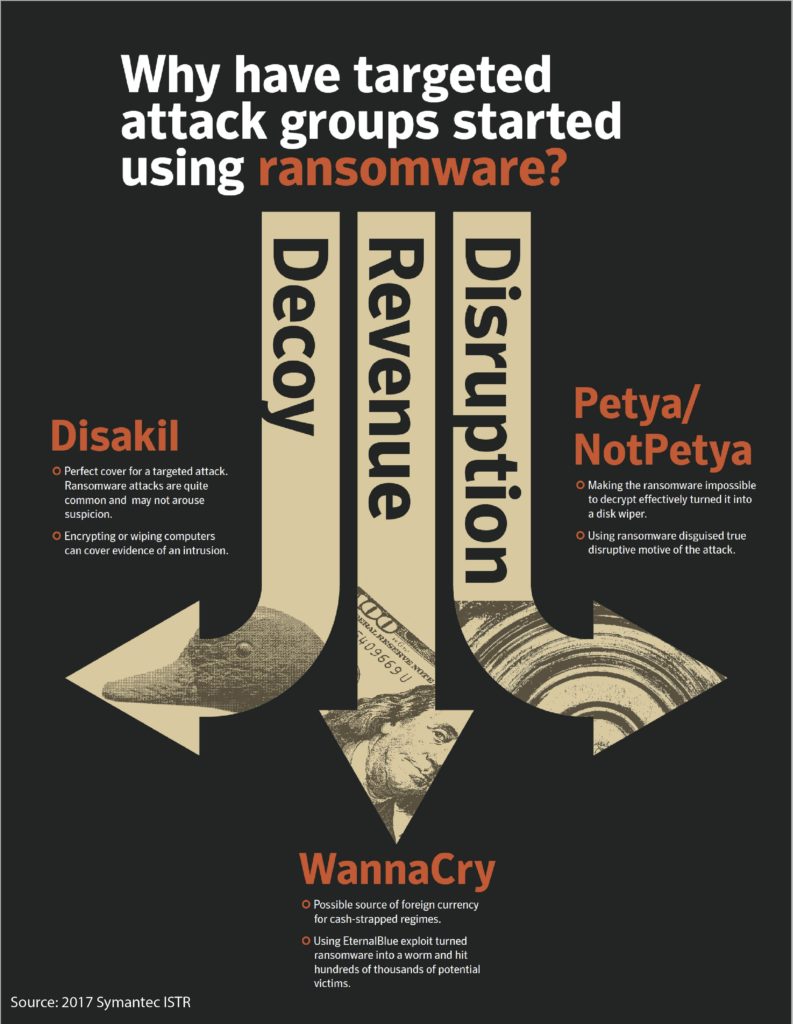
The use of ransomware has exploded in 2017, and with ever increasing use of cloud-based applications, this simple form of malware can paralyze a large company, state or federal agency through locking down system files with powerful encryption. Ransomware no longer serves as a means of revenue for cyber criminals but is also used to serve as a decoy for other directed attacks and even disruption as found in the Petya/NotPetya events. As cybersecurity advances with improved tools and techniques, so do ransomware developers. Michael Nadeau of CSO points out that creators have vastly improved basic elements such as the code writing, but also have figured out that slowing down and randomizing the encryption process further their attempts mostly due to not being detected. Lastly, ransomware developers have implemented a methodology to use decoy ransomware to distract and disrupt a post-attack forensic investigation.
Ransomware’s illusive nature poses a greater threat given the ability to significantly impact critical infrastructure such as local hospital networks and 911 systems. Loss of the ability to access those critical data networks would be catastrophic during normal operating loads, and potentially worse during a crisis event. Ransomware isn’t limited to a specific region of the world either, and the epidemic is primarily focused on technologically developed countries such as Australia, Western Europe, Russia and the United States. Global enterprises were primarily impacted by the three high-pro outbreaks WannaCry, ExPetr and BadRabbit. WannaCry started mid-year 2017 as a worm-like infection propagated through what initially was a Microsoft update. This attack did not focus on any specific industry or group, and eventually affected large organizations such as Renault, Deutsche Bahn and Spain’s primary telecommunications company. Just weeks after WannaCry crated its havoc, ExPetr infiltrated primarily supply chain systems throughout the European continent. The two highest profile victims of ExPetr were Maersk Shipping and FEDEX with loses over $400 Million. BadRabbit occurred later in the year focusing targets in Germany, Turkey, Ukraine and Russia. Throughout all three key events, it is estimated that 65% of world-wide businesses were impacted and 17% of businesses who paid the ransom never recovered their data.
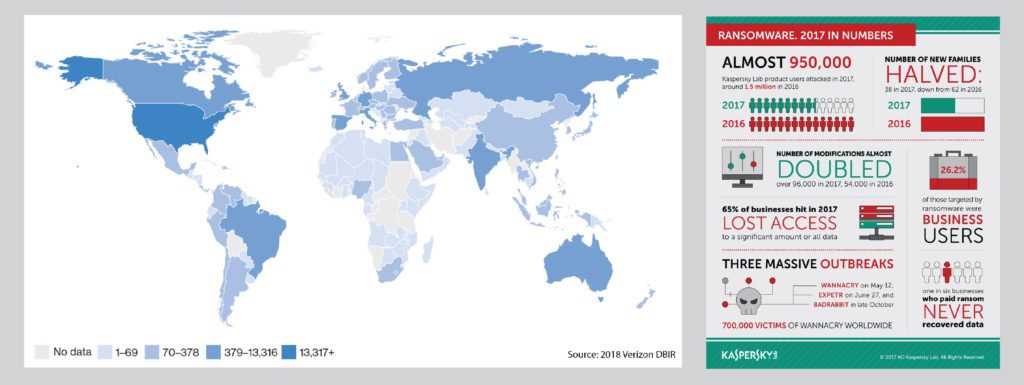
Efforts to thwart malware and ransomware are growing on several fronts. One specific option is Kaspersky’s venture known as nomoreransom.org who can assist victims, provide education and assist in prevention. The key to surviving a malware attack hinges on a comprehensive approach that focuses on defensive and offensive tactics. Adopting policies and procedures that includes employee training and education, regular system maintenance, personnel/system testing and a fully-developed disaster recovery plan will make you a much more hardened target.
III. We’re Not Just Phishing Around
IBM’s annual X-Force report further details that spam mail remains on the rise, and more than half of the overall volume of e-mail received is considered spam, but it is very critical to understand that spam with malicious intent is exponentially increasing as well. This is no longer a simple problem given that e-mail remains a primary attack mechanism to an organization.
Proofpoint identified some 90% of businesses were fraudulently targeted through a variety of methods that included the words ‘REQUEST’, ‘PAYMENT’ or ‘URGENT’ as part of an e-mail. Spoofing of organizational leadership also saw an increase where 57% of targeted companies experienced spoofing of five employees or more.
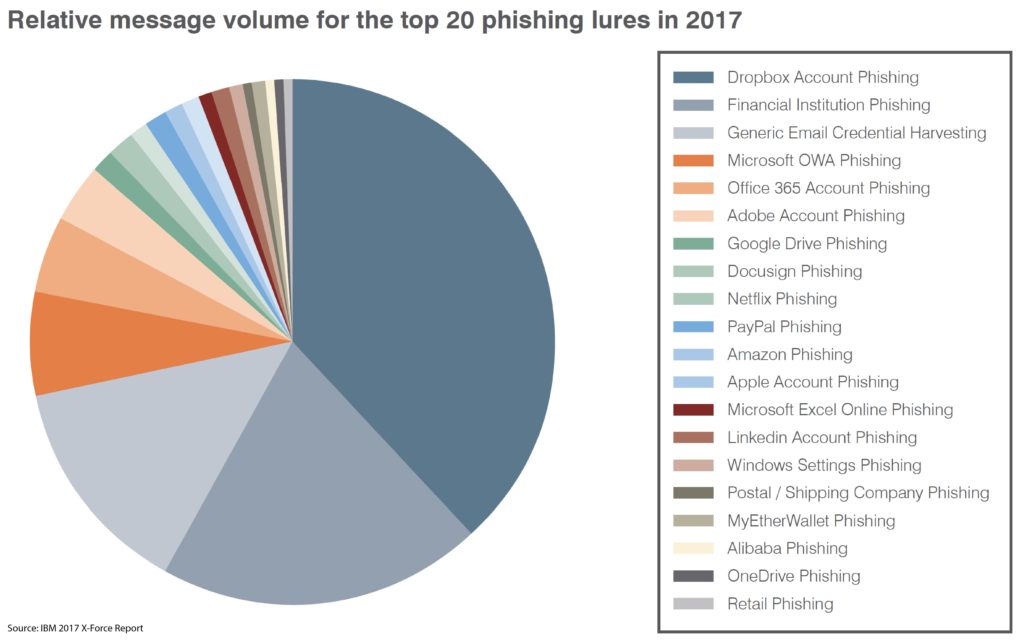
Some of the more prolific attacks of 2016 set phishing on a track to set records, but 2017 proved to be even more ambitious. Phishing isn’t just limited to traditional e-mail anymore but has now can also be employed through text messaging or one of the many instant messaging platforms. That tactic has been labeled ‘smishing’ and have seen a 250% increase according to a Kaspersky Lab’s and Newsweek report.
BEC Hits 50 Countries: More than 500 businesses were victimized from an injected malware used to exploit organizational networks and data. The attack originated in Nigeria with an attachment guiding employees of a company to download what looked like a legitimate attachment
Amazon Prime Phishing Attack: The retail giant was targeted when hackers attempted to gain sensitive payment information through what looked like legitimate Prime purchases
IRS W2 Tax Season: In the United States, attackers spoofed corporate executives requesting personal information for corporate tax compliance purposes. The fraud victimized more than 120,000 individuals and over 100 organizations, and cost taxpayers also through frequently paid tax returns.
History is replete with numerous examples of this successfully proven technique, and it now stands to indicate the numbers will only continue to rise with and move into the mobile device landscape. However, to best defend against this menace it is important to understand the risk you face as you navigate through e-mails, messages and other forms of digital communication. Maintaining updated and patched systems will very likely reduce your vulnerability in addition to regularly backing up your information to a secure location. Finally, combating phishing through effective solutions on premises or in the cloud also can serve to strengthen your defenses and reduce the overall threat.
IV. Manipulation Through Social Engineering
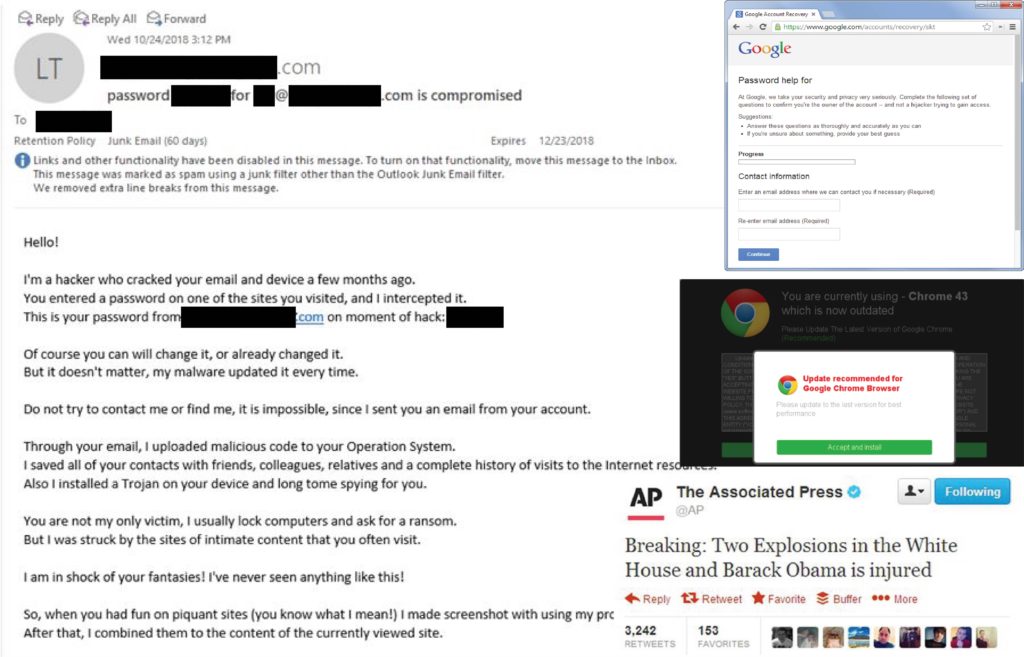
To this point, this report has focused on threats that involve systems and data, but the more important part of the cyber crime equation involves the human factor. Malicious spam campaigns, spear phishing, social media scams and web-based attacks all prey on the natural curiosity and trust humans are born with. This threat very likely poses the greatest risk to systems and data due the insidious psychological nature employed through well-crafted lures and schemes, which have the potential to trick even the savviest of users.
The days of the Nigerian prince e-mail have long passed, and criminals have developed exceptionally sophisticated methods that can include outright deception using a simple lure. A recent example of this tactic included malicious attachments labeled ‘resume.doc’ or ‘invoice.xls’. Another option will present a very high-quality, and sometimes convincing, fraud utilizing legitimate branding and documents that ultimately trick a user to click and unknowingly allow the installation of some form of malware. According to Proofpoint, e-mail remains the top ‘attack vector’. The graphics below clarify the two most prevalent methods of employed and how effective their methods can be.
The According to medium.com, 97% of targeted attacks utilize some form of social engineering. The below facts give a very clear indication as to how truly effective social engineering is.
- Suspiciously registered domains of large enterprises outnumbered BRAND-REGISTERED DOMAINS 20 to 1. That means targets of phishing attacks are more likely to mistake typo-squatted and suspicious domains for their legitimate counterparts.
- Fake browser and plugin updates appeared in massive malvertising campaigns affecting millions of users. As many as 95% of observed web-based attacks like these, including those involving exploit kits, incorporated social engineering to trick users into installing malware rather than relying on exploits with short shelf lives. Two years ago, social engineering in web-based attacks was much less widely deployed.
- About 55% of social media attacks that impersonated customer-support accounts—a trend known as “angler phishing”— targeted customers of financial services companies.
- Some 35% of social media scams that used links and “clickbait” brought users to video streaming and movie download sites. In-browser coin mining, in which attackers hijack victims’ computers to generate cryptocurrency, also went mainstreams. These attacks converged largely around pirated video streaming sites; users’ long viewing sessions gave the miners extended access to victims’ PCs, netting more income for their operators.
Social engineering is very likely the least understood part of cyber crime given the advanced underlying psychological concepts employed. The key here is to ensure all employees are educated in identifying potential attacks that employ a social engineering tactics, techniques and procedures.
V. A Cloudy Outlook
The reality is that unfortunately cybercrime trends appear to be moving in a negative direction, and we fully expect to see more directed attacks and sophisticated tactics. Trends also appear to be almost cyclic in nature in that methods seem to come and go with improving regularity, but there is also strong evidence to argue some techniques will evolve and modify much like the common cold. The fact is that nothing is static in today’s world of information technology.
Looking forward, ransomware will likely remain the top tool for actors despite the initial signs of a cyclic decline. Skimming also has become a key tool to build financial resources within criminal enterprises, which will only fuel more Distributed-Denial of Service (DDoS) attacks on public and private organizations. Supporting all of this is the ever-present threat of social engineering and its insidious methods to ultimately bilk the savviest users of their finances, personal information and accounts.
Fact is, history does serve as an excellent tool to predict the future, but innovative thinking and creative system management are also paramount if we are to prepare or even prevent the next major disruption. A quick review of the facts identify that social attacks were utilized in 43% of all breaches, and almost all phishing attacks that led to a breach were followed with some form of malware, and 28% of phishing breaches were targeted. Phishing is the most common social tactic (93% of social incidents). It is safe to say that then new frontier in cyber crime is surely pointing to mobile devices, but not just the smart phone or tablet we have become absolutely dependent on. We are a connected society through our vehicles and digitally-controlled medical devices, and those devices could potentially be taken over by bad actors for a variety of reasons. All hope isn’t lost, as the information presented should provoke thought and drive action to focus on application of technology and education intended to fight a growing epidemic. Much like a military leader planning for battle, we must prepare ourselves for the fight, and ensure we don’t take a knife to a gun fight.